How Fashion Companies Can Protect Sensitive Data with CUI Enclaves and NIST Standards
The fashion industry has become a prime target for cyberattacks. Design files, supplier agreements, customer databases, and proprietary research represent high-value intellectual property that competitors and cybercriminals alike seek to exploit. As digital transformation accelerates across the sector, fashion companies face mounting pressure to secure their most sensitive information against increasingly sophisticated threats.
This challenge has brought Controlled Unclassified Information (CUI) protocols into sharper focus. CUI refers to sensitive data that requires safeguarding or controlled dissemination according to laws, regulations, and government policies. For fashion enterprises working with government contracts or handling particularly sensitive commercial data, understanding CUI protection frameworks has become essential to maintaining competitive advantage and customer trust.
What Is a CUI Enclave?
A CUI enclave functions as a dedicated security environment designed specifically to store and manage Controlled Unclassified Information. These protected systems employ multiple layers of defense to prevent unauthorized access and mitigate cyber threats. In fashion contexts, CUI might encompass:
- Design schematics and technical specifications
- Supplier contracts and manufacturing agreements
- Customer databases containing personal information
- Proprietary research and development documentation
- Strategic business plans and market analysis
Establishing a functional CUI enclave requires implementing strict access controls, encryption protocols, and continuous security monitoring. The Federal Acquisition Regulation CUI requirements provide detailed guidance on handling this category of data. Fashion companies that adopt these frameworks can better protect their intellectual property while demonstrating compliance with industry standards that increasingly matter to partners and clients.
Understanding CMMC Levels and Cybersecurity Maturity
The Cybersecurity Maturity Model Certification (CMMC) establishes a tiered framework for evaluating and improving organizational cybersecurity practices. While originally developed for defense contractors, these standards offer valuable benchmarks for any fashion company handling sensitive information.
The original CMMC framework defined five progressive levels:
- Level 1: Basic Cyber Hygiene — Focuses on fundamental security practices including regular software updates, antivirus protection, and basic access controls
- Level 2: Intermediate Cyber Hygiene — Requires documented security policies and more sophisticated protective measures
- Level 3: Good Cyber Hygiene — Demands comprehensive risk management programs and continuous monitoring capabilities
- Level 4: Proactive — Organizations must actively enhance defenses against both known and emerging threats
- Level 5: Advanced/Progressive — Involves optimizing cybersecurity processes and deploying cutting-edge security technologies
Achieving higher CMMC levels signals a serious commitment to data protection. For fashion businesses, this certification can strengthen relationships with security-conscious partners and differentiate brands in an increasingly risk-aware marketplace.
CMMC 2.0: A Streamlined Approach
The updated CMMC 2.0 framework simplifies certification while maintaining robust security requirements. Key changes from the original model include:
- Consolidated Levels — Reduces complexity by condensing five levels into three focused tiers
- Self-Assessment Options — Allows smaller organizations to self-certify at lower levels, reducing administrative burden
- Flexible Implementation — Accommodates different business sizes and operational models
- Clearer Requirements — Provides more specific guidance on meeting each level’s standards
For fashion enterprises, CMMC 2.0 compliance delivers several strategic advantages. Enhanced security measures provide stronger protection against data breaches and intellectual property theft. Alignment with recognized standards strengthens credibility with business partners. The streamlined certification process also reduces time and resource investments compared to the original framework.
Navigating CMMC Certification Costs
Pursuing CMMC certification requires careful financial planning. The process involves multiple stages, each with associated expenses that fashion companies should anticipate:
- Initial Assessment — Evaluating current cybersecurity posture against target CMMC level requirements.
- Gap Remediation — Implementing necessary improvements to meet certification standards.
- Third-Party Evaluation — Engaging certified assessors to validate compliance. CMMC certification consultants like Cuick Trac, Totem, and Redspin can help organizations prepare documentation and evidence packages before a formal third-party assessment, reducing the likelihood of findings that extend the timeline and add cost.
- Documentation Development — Creating comprehensive evidence of security controls and policies.
Cost factors vary considerably based on organizational complexity:
- Assessment Fees — External assessor costs scale with system complexity and certification level.
- Technology Investments — New security tools, infrastructure upgrades, and software licenses.
- Training Expenses — Employee education programs and ongoing awareness initiatives.
- Maintenance Costs — Continuous monitoring, periodic reassessment, and compliance updates.
Fashion companies can manage these expenses through strategic planning. Starting the certification process early allows costs to be distributed over time. Some organizations may qualify for government grants or incentives supporting cybersecurity improvements. Prioritizing high-impact security investments that address the most significant risks can also optimize resource allocation.
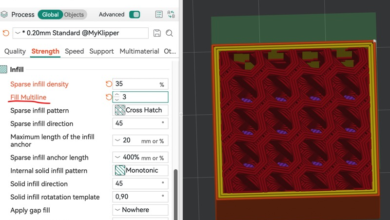
Implementing NIST Compliance Solutions
The National Institute of Standards and Technology (NIST) provides comprehensive frameworks for protecting sensitive information. NIST 800-171 specifically addresses security requirements for organizations handling Controlled Unclassified Information, making it particularly relevant for fashion companies working with government contracts or managing highly sensitive commercial data.
NIST compliance solutions offer structured approaches to data protection:
- Access Control — Limiting system access to authorized users and processes
- Awareness and Training — Ensuring personnel understand security responsibilities
- Audit and Accountability — Creating and protecting audit records to enable security monitoring
- Configuration Management — Establishing and maintaining baseline configurations
- Identification and Authentication — Verifying user and device identities
- Incident Response — Establishing capabilities to detect, report, and respond to security incidents
- Maintenance — Performing periodic and timely system maintenance
- Media Protection — Protecting information in printed or digital media
- Personnel Security — Ensuring individuals occupying positions of responsibility are trustworthy
- Physical Protection — Limiting physical access to information systems and facilities
- Risk Assessment — Periodically assessing operational risks
- Security Assessment — Periodically assessing security controls
- System and Communications Protection — Monitoring and controlling communications at system boundaries
- System and Information Integrity — Identifying and managing information system flaws in a timely manner
Fashion companies can implement NIST 800-171 compliance through a systematic approach. Begin with a gap analysis comparing current practices against NIST requirements. Develop a comprehensive security plan addressing identified deficiencies.
Building an Effective NIST Compliance Checklist
A well-structured compliance checklist helps fashion companies systematically address NIST requirements. Consider these essential steps:
- Requirement Identification — Review the 14 families of security requirements outlined in NIST 800-171 and determine which apply to your specific operations
- Current State Assessment — Evaluate existing cybersecurity measures against NIST standards, documenting gaps and vulnerabilities
- Policy Documentation — Develop written policies covering access control, incident response, data protection, and other required areas
- Technical Control Implementation — Deploy necessary security technologies including encryption, multi-factor authentication, and monitoring systems
- Personnel Training — Conduct regular education sessions ensuring team members understand cybersecurity best practices and their compliance responsibilities
- Continuous Monitoring — Establish processes for ongoing security assessment and threat detection
- Regular Review and Updates — Periodically revisit your compliance checklist to address emerging threats and regulatory changes
Many organizations benefit from working with a NIST 800-171 compliance consultant who can provide tailored guidance based on specific business needs and industry context. These specialists help navigate complex requirements and develop practical implementation strategies.
Real-World Benefits for Fashion Companies
Fashion enterprises that implement CUI enclaves and achieve CMMC and NIST compliance realize tangible advantages:
- Reduced Breach Risk — Comprehensive security frameworks significantly decrease the likelihood of data breaches that could expose design files, customer information, or strategic plans
- Enhanced Brand Reputation — Demonstrating serious commitment to cybersecurity builds trust with customers, partners, and investors
- Regulatory Compliance — Meeting federal standards becomes essential for companies pursuing government contracts or working with defense-related textiles
- Competitive Differentiation — Security-conscious consumers and business partners increasingly favor companies with verified cybersecurity credentials
- Intellectual Property Protection — Robust security measures safeguard the design innovations and proprietary processes that drive competitive advantage
- Operational Resilience — Strong cybersecurity foundations enable faster recovery from security incidents and reduce business disruption
The investment in cybersecurity infrastructure pays dividends beyond mere compliance. As cyber threats continue evolving, fashion companies with mature security practices will be better positioned to protect their innovations, maintain customer trust, and capitalize on opportunities requiring demonstrated data protection capabilities.
For fashion businesses navigating these complex requirements, the path forward involves assessing current capabilities, identifying gaps, and systematically implementing the controls necessary to protect sensitive information. Whether pursuing formal CMMC certification or adopting NIST frameworks as internal standards, the goal remains consistent: building resilient security practices that safeguard the intellectual property and customer data that drive business success.